.Net Software Obfuscator from Rustemsoft
Skater.NET Obfuscator came up as a response to a need expressed by Rustemsoft, which was having difficulty effectively protecting.NET applications.

A method of protecting software from unauthorized attempts at reverse engineering is known as code obfuscation.
It is possible to determine that any software protection technique's primary function is detecting pirate attempts to decipher or tamper with the software. Protecting the software against such endeavors and modifying the software to ensure that its functionality degrades in an undetectable manner if the defense fails are also critical.
When you start Skater GUI you can open your target .NET assembly on the first screen.
It is possible to determine that any software protection technique's primary function is detecting pirate attempts to decipher or tamper with the software. Protecting the software against such endeavors and modifying the software to ensure that its functionality degrades in an undetectable manner if the defense fails are also critical.
When you start Skater GUI you can open your target .NET assembly on the first screen.
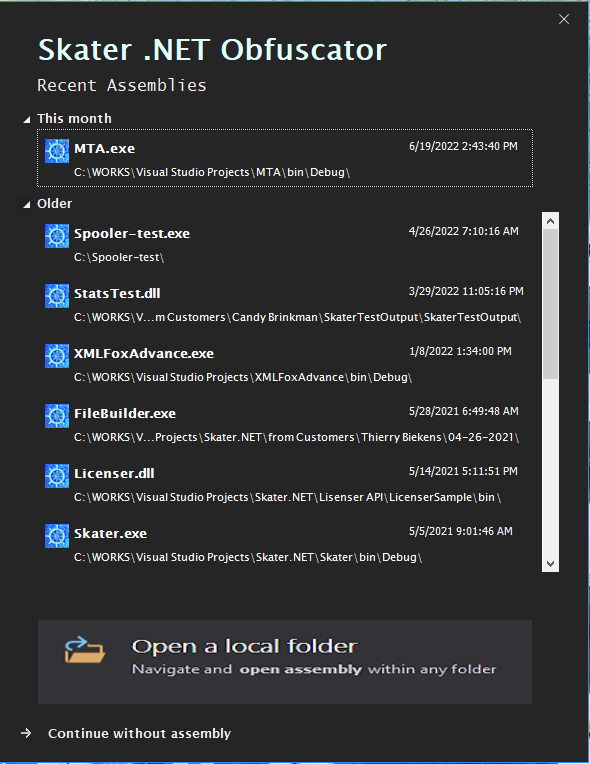
You can select an assembly that was already obfuscated before. Otherwise, you have a choice to open a new .NET dll or exe by clicking the ‘Open a local folder’ dialog box.
Why our .NET Obfuscator is an all-inclusive and professional solution for our protect .NET project:
Stops Reverse Engineering
Skater.NET Obfuscator is an obfuscation tool that is useful for our .NET code protection. It employs every software protection technique and obfuscation algorithm that is currently known. Protecting Microsoft.NET framework applications from unauthorized code extraction and reverse engineering is simple when you use a tool like Skater.NET Obfuscator.
Source Code Protection
To successfully protect your programs with professional software, developers do not need to make any changes to the source code or have any prior programming experience. Skater.NET Obfuscator will reconstruct your.NET assemblies into a new view that is incomprehensible. This new view will be impossible to understand.
Command-Line Interface
It is highly beneficial to run the command-line version of Skater in batch mode for your regularly scheduled product updates. To begin, you must assign an assembly setting using the GUI version. The settings will be necessary for the batch obfuscate task after that. The Skater .NET Obfuscator free is the tool you need if you want to obfuscate the.NET products you sell periodically.
In Conclusion,
We focus on the tools that attackers employ and ensure that our defenses are always up to date to deal with any new developments. When an app has protections like these layered on top of each other, it becomes nearly impossible to attack the app because every time an attacker tries to attack one layer of protection, another layer is there to prevent them from doing so.
Why our .NET Obfuscator is an all-inclusive and professional solution for our protect .NET project:
Stops Reverse Engineering
Skater.NET Obfuscator is an obfuscation tool that is useful for our .NET code protection. It employs every software protection technique and obfuscation algorithm that is currently known. Protecting Microsoft.NET framework applications from unauthorized code extraction and reverse engineering is simple when you use a tool like Skater.NET Obfuscator.
Source Code Protection
To successfully protect your programs with professional software, developers do not need to make any changes to the source code or have any prior programming experience. Skater.NET Obfuscator will reconstruct your.NET assemblies into a new view that is incomprehensible. This new view will be impossible to understand.
Command-Line Interface
It is highly beneficial to run the command-line version of Skater in batch mode for your regularly scheduled product updates. To begin, you must assign an assembly setting using the GUI version. The settings will be necessary for the batch obfuscate task after that. The Skater .NET Obfuscator free is the tool you need if you want to obfuscate the.NET products you sell periodically.
In Conclusion,
We focus on the tools that attackers employ and ensure that our defenses are always up to date to deal with any new developments. When an app has protections like these layered on top of each other, it becomes nearly impossible to attack the app because every time an attacker tries to attack one layer of protection, another layer is there to prevent them from doing so.
